Since github.com is about to disallow basic authentication using login and password over http/https connections, you should switch to connect via ssh providing a public ssh-key together with a passphrase.
In this post I describe the steps necessary when using git for windows, however the steps are probably more or less identical if you’re running the git commands in any linux shell.
1. Create your private SSH-Key
In order to connect via ssh to github, you need to have a pair of keys. A private key which should never be given out to others, and a matching public key, which can later be uploaded to github to enable it, that your commits and pushes are coming from you.
If you already have generated a pair of ssh keys, you can skip this step and go directly to step 2). Otherwise now open your git-bash console anywhere in your filesystem and type the following:
$ ssh-keygen -t rsa -b 4096 -C "your-email@yourdomain.com"“Detail for the intrigued: If you want to go for security, don’t use RSA keys anymore, since they’ve been proven to be vulnerable. Rather use the ed25519 elliptic curve encryption, which is considered to be more secure. However, if you’re using old-fashioned or less security-aware IDEs like RStudio, you still might have to go for RSA.”
Fabian Leuthold
You’ll get first prompted with the following question about where to store the private/public key-pair:
$ ssh-keygen -t rsa -b 4096 -C "your-email@yourdomain.com"
Generating public/private rsa key pair.
Enter file in which to save the key (/c/Users/your.user/.ssh/id_rsa):
If the path shown has been correctly chosen – it should point to your local user folder on your machine – hit enter, otherwise provide the desired location and confirm it with enter.
If you haven’t yet stored a pair of keys there, you’ll be asked to provide a passphrase. The passphrase is needed to protect (encrypt) the private key and it reduces risks if it should get stolen. However, if you provide one, you’ll be required to take an additional step as described in Step 6) in this instruction here.
If you decide to provide a passphrase, enter it twice – and make sure you remember it (If you provide one, you’ll be prompted everytime, unless you perform additional steps using the ssh-agent in order to automatically provide the password). Otherwise just hit enter:
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
After successfully providing two times the same passphrase you’ll get an output indicating, that everything went right. It should look something like this:
Your identification has been saved in /c/Users/your.user/.ssh
Your public key has been saved in /c/Users/fabian.leuthold/.ssh/id_rsa.pub
The key fingerprint is:
SHA256:T5ZEn9e3pHLEajr2ka37wmWlu+wVg3dygwbu2mgZM9C
{some account information and E-Mail}
The key's randomart image is:
+---[RSA 3072]----+
| .... . |
| o. . . = |
| .o . = |
| .o. + o |
|o o. S.+.+ . |
| o .o+ =+o . |
|.o= ++Q...+o. |
|o+.=+ ...+= |
|+o.=. . .o |
+----[SHA256]-----+Otherwise you’ll be prompted, whether you want to overwrite your existing keys:
/c/Users/your.user/.ssh/id_rsa already exists.
Overwrite (y/n)?
Type ‘y’ and hit enter to overwrite your local keys, if you don’t remember the passphrase for these earlier generated keys and want to generate an new pair of keys, otherwise type ‘n’ and press enter.
Now type ‘cd ~/.ssh’ and hit enter, in order to navigate to your home location or cd to the location you provided to store the key-pair, if you have provided another file-location above. Then type ‘cat id_rsa.pub’ and hit enter. You should see an output like the following:
$ cat id_rsa.pub
ssh-rsa 8wVQZKjeGcjDOL5UlsuusFncCzWBQ7RKNUSesmQRMSGkVb1/3j+skZ6UtW+5u09lHNsj6tQ51s1SPrCBkedbNf0Tp0GbMJDyR4e9T04ZZwIDAQABAoGAFijko56+qGyN8M0RVyaRAXz++xTqHBLh3tx4VgMtrQ+WEgCjhoTwo23KMBAuJGSYnRmoBZM3lMfTKevIkAidPExvYCdm5dYq3XToLkkLv5L2pIIVOFMDG+KESnAFV7l2c+cnzRMW0+b6f8mR1CJzZuxVLL6Q02fvLi55/mbSYxECQQDeAw6fiIQXGukBI4eMZZt4nscy2o12KyYner3VpoeE+Np2q+Z3pvAMd/aNzQ/W9WaI+NRfcxUJrmfPwIGm63ilAkEAxCL5HQb2bQr4ByorcMWm/hEP2MZzROV73yF41hPsRC9m66KrheO9HPTJuo3/9s5p+sqGxOlFL0NDt4SkosjgGwJAFklyR1uZ/wPJjj611cdBcztlPdqoxssQGnh85BzCj/u3WqBpE2vjvyyvyI5kX6zk7S0ljKtt2jny2+00VsBerQJBAJGC1Mg5Oydo5NwD6BiROrPxGo2== your-email@yourdomain.com
Congrats! Now you’ve successfully configured a pair of private/public keys. Copy this text to your clipboard. Make sure to select the whole public key, starting with “ssh-rsa” and ending with your E-Mail address.
3. Upload your Public Key to github
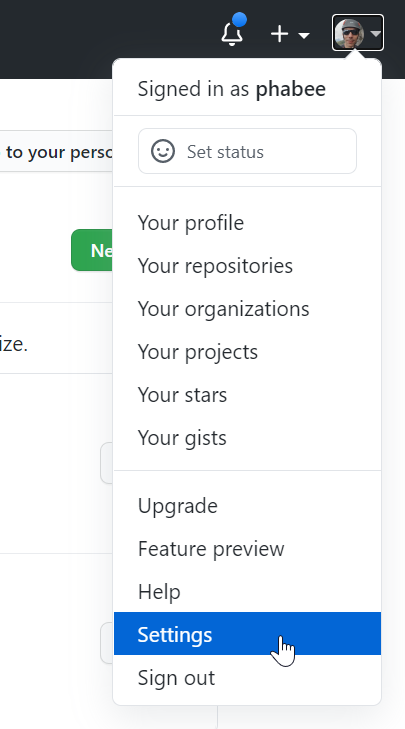
In order for github to be able to validate content encrypted with your private key, you have to provide the public key on the github platform. Now go to the browser and connect to github using your account (login/pwd) and navigate to your settings page. Click on your user-Icon and choose ‘settings’:
Then you’ll see another navigation menu appearing. Choose “SSH and GPG Keys”. On the page appearing, click “New SSH key”, then provide a Title for this Public key, which reminds you, to which machine this key is tied to (i.e. “my first pink laptop”), in the Key-field paste your public key, you’ve copied to your clipboard before. This should look somethin like this:
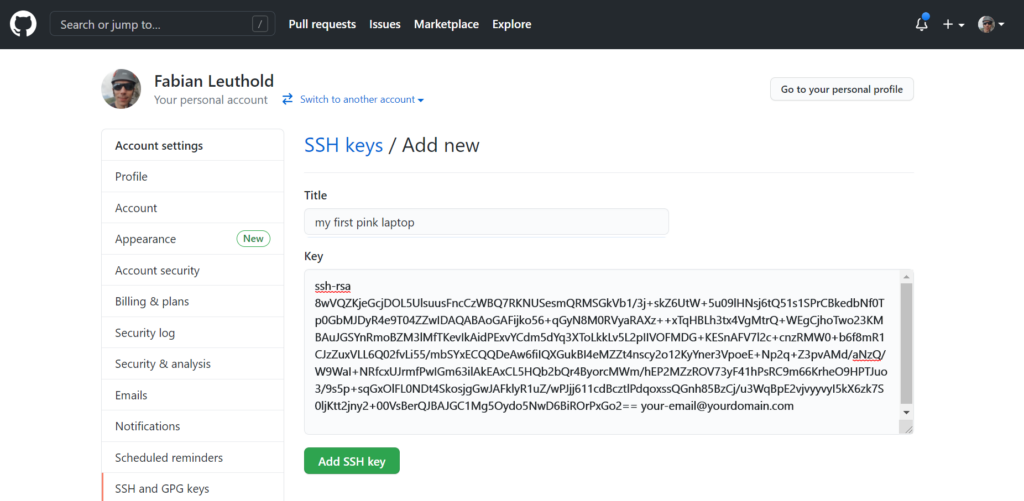
Now confirm adding the new key by hitting the “Add SSH Key” button.
Congrats! You’ve successfully configured github to identify your ssh-key.
4. Reconnect a local Repository for Using SSH-Connection
To migrate an existing repository for using ssh-conneciton you can either migrate it as described in this section or delete the repository from your local machine – do this only, if no local uncommitted and unpushed changes have been applied – and clone it as described in the next section 5).
If you have local repositories on your computer you’d like to connect to your remote location on github using ssh instead over the older http/https protocol, perform the following steps for each repository, you want to reconnect using the more secure ssh-protocol:
Change to the repository you want to reconnect – here we assume your repository is called “repo-name” and type ‘git remote -v’. You should see the following output:
domainuser@hostname MINGW64 ~/repo-name (master)
$ git remote -v
origin https://github.com/mygit-account/repo-name.git (fetch)
origin https://github.com/mygit-account/repo-name.git (push)
The output is telling you, that you have configured the remote origin to be connected over https. Since this is deprecated, we want to connect via ssh instead, that’s what we have prepared the keys for and provided the public key to github.
In order to wire the new ssh-origin, we have to remove the old remote https-configuration using the ‘git remote rm origin’ command as shown here:
$ git remote rm originNow switch to github in your webbrowser and navigate to the repository location of the repository, you want to reconnect via ssh (we assume here the project is called ‘repo-name’):
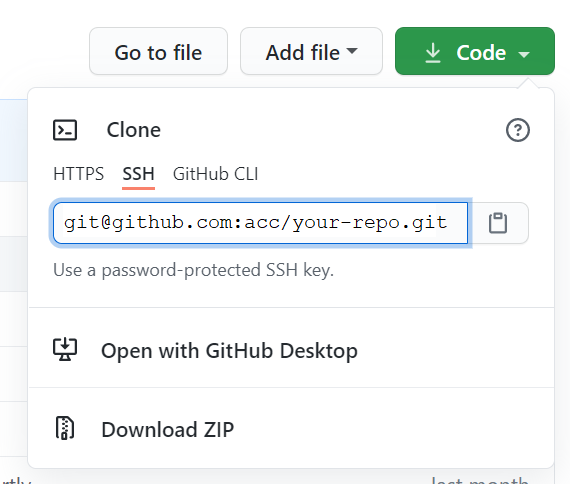
Now click the clipboard-icon next to the ssh-url on your github repository base-site to copy the url into your clipboard, then return to your git-shell and type ‘git remote add origin ‘ and paste your ssh-location URL from your clipboard. You’ll then see something like this:
git remote add origin git@github.com:acc/your-repo.gitNow you can check, whether your remote location has been successfully configured by typing ‘git remote -v’ again. You should see two entries starting with ‘origin git@github.com…’ now.
Now it’s a good idea to make some minor change to the repository and push it to the remote location, in order to validate and store the remote location on your host. For this purpose make a minor change i.e. to a textfile, commit the changes and push it to the newly configured ssh-remote location master branch as follows:
$ git push
fatal: The current branch master has no upstream branch.
To push the current branch and set the remote as upstream, use
git push --set-upstream origin masterThe error tells you, what to do, so do as indicated. You should see some message as follows:
$ git push --set-upstream origin master
The authenticity of host 'github.com (140.82.121.3)' can't be established.
RSA key fingerprint is SHA256:nThbg6kXUpJWGl7E1IGOCspRomTxdCARLviKw6E5SY8.
Are you sure you want to continue connecting (yes/no/[fingerprint])? Now check the SHA256 Key provided to be identical as the key shown above. For more details refer to this page, where the recent public-keys of the github servers can be found. It makes sense to check this key to be sure, that you don’t get spoofed with a fake github server and i.e. aknowledgeing and storing an invalid ip-address to a compromitted server. If the key is correct, type ‘y’ or ‘yes’ and hit enter:
(yes/no/[fingerprint])? yes
Warning: Permanently added 'github.com,140.82.121.3' (RSA) to the list of known hosts.This message tells you, that you confirmed having checked the identity of the github server and the IP indicated can be added to the list of known hosts.
Now you’ll get prompted to enter the passphrase for your (private) key. Enter your passphrase, then the push shall succeed and show something like the following output:
Enter passphrase for key '/c/Users/fabian.leuthold/.ssh/id_rsa':
Enumerating objects: 8, done.
Counting objects: 100% (8/8), done.
Delta compression using up to 8 threads
Compressing objects: 100% (6/6), done.
Writing objects: 100% (6/6), 580 bytes | 580.00 KiB/s, done.
Total 6 (delta 4), reused 0 (delta 0), pack-reused 0
remote: Resolving deltas: 100% (4/4), completed with 2 local objects.
To github.com:youraccount/your-repo.git
39b3072..85f5ed2 master -> master
Branch 'master' set up to track remote branch 'master' from 'origin'.Congrats! You’ve now successfully configured your git repository to use ssh instead of http/https!
5. Clone an existing remote Repository
This is easier and similar to the steps above. Typ ‘git clone ‘ followed by the clone ssh-url from github, shown in the screenshot:
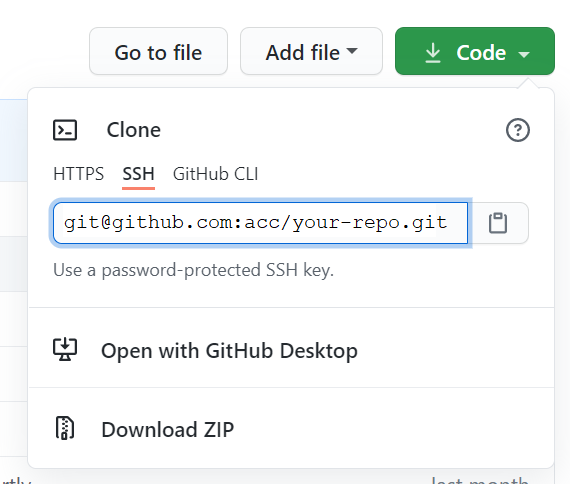
The git-shell command should look something like this:
$ git clone git@github.com:youraccount/your-repo.git
Cloning into 'your-repo'...
Enter passphrase for key '/c/Users/your.user/.ssh/id_rsa':
remote: Enumerating objects: 35, done.
remote: Counting objects: 100% (35/35), done.
remote: Compressing objects: 100% (26/26), done.
remote: Total 130 (delta 12), reused 25 (delta 8), pack-reused 95
Receiving objects: 100% (130/130), 3.62 MiB | 2.28 MiB/s, done.
Resolving deltas: 100% (53/53), done.
After confirming the command you’ll be asked to provide the pass-phrase. If you’ve successfully provided the passphrase, the project will be pulled and cloned into your local repository.
Hooray, you’re done! 🙂
If you have chosen to encrypt your key using a passphrase and you do not want to type in the passphrase for every push, continue with step 6).
6) Add ssh-key to ssh-agent
If you’re using a linux, it’s all very simple. Details see here. However, with windows things are a bit more complicated. From the git-scm installation you should have a service called ‘OpenSSH Authentication Agent’. Open the Services-Window by hitting the windows-key and typing ‘services’.
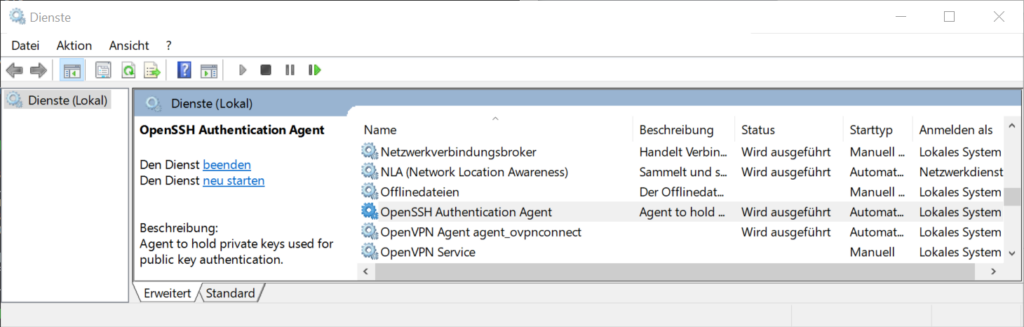
There you should find the ‘OpenSSH Authentication Agent’. Set the starting-type to ‘Automatic’ and make sure it’s started.
Then switch to your git-shell and type:
eval `ssh-agent -s`; ssh-add KEY_LOCATIONKEY_LOCATION is the path and filename pointing to your private key. If you generated an rsa key and have default path configurations, this would typically be ‘~/.ssh/id_rsa’. On the console you should then see something like this:
$ eval `ssh-agent -s`; ssh-add ~/.ssh/id_rsa
Agent pid 2061
Enter passphrase for /c/Users/your_user/.ssh/id_rsa:
Identity added: /c/Users/your_user/.ssh/id_rsa (your-email@yourdomain.com)
Congrats! Now you’ve successfully added your new ssh-key to the Authentication Agent and won’t have to provide the securephrase in order to connect to the github server anymore.